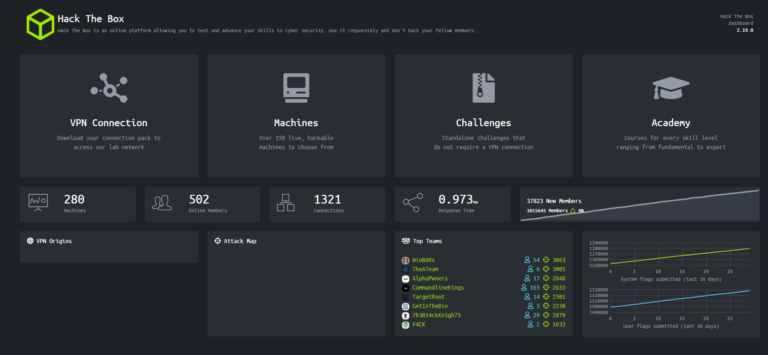
HackTheBox retired machine writeups
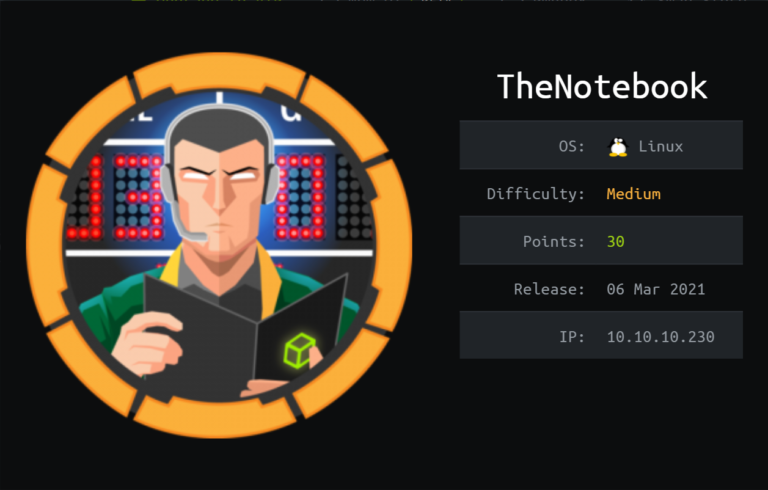
Hackthebox retired machine are those machines which are not active on the Hackthebox . But the good thing about the retired machines is that the writeups for hackthebox retired machines are available . So the beginners who are starting the CTF journey can read these writeups and get the idea how the machines are solved .